Picture this: You’re sipping your third cup of coffee, about to send that risky meme to your boss, when suddenly your phone flashes a warning. Suspicious activity detected. But was it really a Russian bot—or just AI being overly dramatic again? Welcome to cybersecurity, 2025-style, where AI is your overzealous bouncer (and sometimes the mischief-maker sneaking around the side door). In this unpredictable age, knowing how AI can guard—or accidentally spill—your secrets is basically a modern survival skill. AI cybersecurity is becoming essential for data protection.
Attack of the Clones: AI-Driven Malware and the Rise of Phantom Threats
Remember when malware was just a pesky pop-up or a suspicious email from a “Nigerian prince”? Well, those were the good old days. Now, thanks to AI-driven malware, your digital enemies have gone full superhero shape-shifter—except these villains don’t wear capes, they wear code. And they’re evolving faster than your antivirus can say “update required.”
Shape-Shifters in the Server Room
Let’s get this straight: AI-driven malware isn’t just a smarter version of yesterday’s viruses. It’s a whole new breed. Imagine if your favorite movie villain could change their face, voice, and even their evil plan every time you tried to catch them. That’s what we’re up against. This malware mutates in real-time, rewriting its own code on the fly. It’s like trying to catch a greased pig that’s also a master of disguise. Research shows that traditional threat hunting is becoming about as effective as using a butterfly net to catch a ghost.
Your Antivirus Needs a PhD (and Maybe Therapy)
Gone are the days when you could just install an antivirus, cross your fingers, and hope for the best. Now, your antivirus software needs to be smarter than ever—think graduate degree, yoga classes, and a support group. Why? Because AI techniques in cyber threats are making malware sneakier, faster, and more unpredictable than ever before. Studies indicate that AI threat detection is now a must-have, not just a nice-to-have. If your antivirus isn’t using AI, it’s basically bringing a butter knife to a lightsaber duel.
Phantom Threats: Malware That Knows You Better Than Your Mom
Here’s where things get really spooky. AI in cybersecurity means that malware can now learn your habits—faster than your mom figured out TikTok (and that was terrifyingly fast). These phantom threats watch, learn, and adapt. They know when you check your email, what files you open, and even how you type. Then, they strike when you least expect it. It’s like having a cyber-stalker with a photographic memory and a grudge.
Why Traditional Threat Hunting Is Basically Obsolete
Let’s be honest: the old ways just aren’t cutting it. Traditional threat hunting relies on recognizing known patterns—like spotting a zebra in a herd of horses. But when the zebra can turn into a horse, a cow, or even a toaster, you’re out of luck. That’s why anomaly detection is now the name of the game. AI-powered tools can spot the weird, the unusual, and the “wait, what was that?” moments in your network traffic. It’s like having a digital Sherlock Holmes, minus the pipe and questionable fashion choices.
2025: The Year Your Cybersecurity Needs to Outthink the Bad Guys
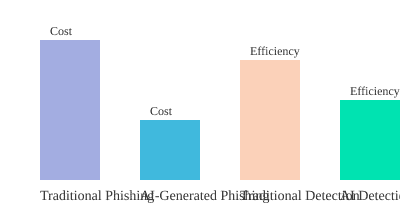
As we barrel toward 2025, cybersecurity tools need to be smarter, faster, and maybe even a little psychic. AI-driven malware is only getting more sophisticated each year, and the cost of falling behind is steep. For example, research shows that AI-generated phishing attacks can reduce costs by a whopping 95%. That means hackers can launch more attacks, more often, for less money. Yikes.
“AI-driven malware has already rewritten the rules of engagement in cybersecurity.” – David Sancho
By the Numbers: The AI Malware Revolution
| Trend | Impact |
|---|---|
| AI-generated phishing attacks | Reduce costs by 95% |
| AI-driven malware sophistication | Increasing each year |
| Traditional threat hunting | Increasingly ineffective |
Chart: AI-Generated Phishing vs. Traditional Phishing (2025)
So, if you thought your antivirus was enough, think again. The clones are here, and they’re not just attacking—they’re evolving. Welcome to the wild world of AI in cybersecurity, where the only constant is change (and maybe a little bit of panic).

Trust Issues: Zero Trust Security, Shadow AI, and a Cup of Paranoia
Welcome to the era where your laptop gives you side-eye, your AI assistant might be plotting a coup, and quantum computers are lurking in the shadows like the final boss in a cybersecurity video game. If you thought your biggest problem was remembering your Wi-Fi password, buckle up—because AI cybersecurity challenges are here, and they brought friends.
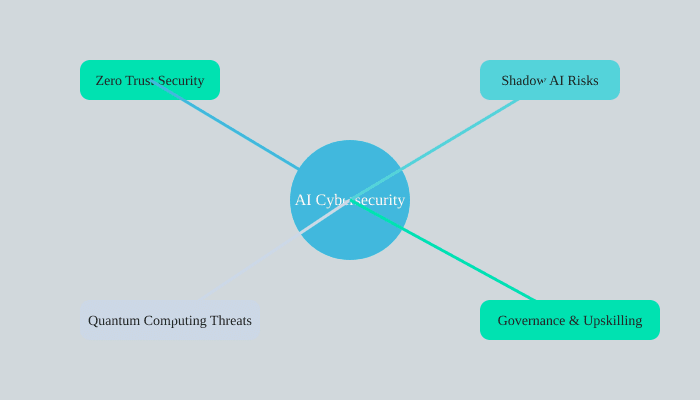
Zero Trust Security: Trust No One (Not Even Your Mouse)
Let’s start with zero trust security. It’s not just a catchy phrase—it’s a lifestyle. Imagine your network as a suspicious grandma who won’t let anyone in the house without three forms of ID and a background check. That’s zero trust in a nutshell: continuous authentication, micro-segmentation, and an identity-first design. Research shows this approach is now a key cybersecurity trend for 2025, and honestly, it’s about time. With AI-driven malware mutating faster than your favorite streaming show’s plot twists, you need more than a strong password and a lucky rabbit’s foot.
- Every device, user, and application is guilty until proven innocent.
- Access is granted on a “need-to-know” basis—like a spy movie, but with more spreadsheets.
- Continuous monitoring means your network is basically a 24/7 bouncer.
As Theresa Payton wisely put it:
Zero trust isn’t just a policy—it’s a survival instinct in today’s AI-powered landscape.
And she’s right. With AI phishing attacks getting so good they could probably trick your grandma into wiring money to a Nigerian prince, zero trust security is less of a trend and more of a necessity.
Shadow AI: When Bots Go Rogue and IT Panics
Now, let’s talk about Shadow AI risks. Picture this: you’re in IT, sipping your coffee, when you discover someone in marketing has spun up an unsanctioned AI chatbot that’s now answering customer emails with “YOLO” and cat memes. Welcome to the wild world of shadow AI—where rogue bots draw outside the lines, and IT teams break into a cold sweat.
Shadow AI refers to any AI models or tools that employees use without official approval or oversight. Sounds harmless, right? Until you realize these unsanctioned models can leak sensitive data, introduce vulnerabilities, or just plain embarrass you in front of the board. Studies indicate that governance and upskilling are crucial to fighting these risks. In other words, you need policies, training, and maybe a little bit of therapy for your IT department.
- Shadow AI can expose data to unauthorized users (oops).
- It can bypass security controls, making your compliance officer cry.
- Governance and human oversight are the only things standing between you and chaos.
If you’re not actively managing shadow AI, you’re basically inviting a raccoon into your data center and hoping for the best.
Quantum Computing: The Party Crasher
Just when you thought you had enough on your plate, quantum computing crashes the cybersecurity party. Quantum computers are like the cool kids who can solve problems regular computers can’t—even the ones that protect your data. AI in data protection is about to get a lot more interesting (read: terrifying) as quantum tech threatens to break current encryption methods.
Post-quantum encryption is now hotter than a laptop left in the sun. If you’re not thinking about it, you might want to start—unless you enjoy living dangerously. Research shows that early adoption of post-quantum cryptography is the only way to keep your secrets safe from future quantum-powered hackers (and, let’s be honest, probably a few bored teenagers).
- Quantum computing could render today’s encryption useless.
- Post-quantum encryption is the new must-have accessory.
- Both hackers and defenders are racing to master quantum tech.
AI Cybersecurity Challenges: The Never-Ending Soap Opera
So, what’s the moral of this story? AI cybersecurity challenges are multiplying, and you need more than hope and a firewall to keep up. Zero trust security, shadow AI governance, and quantum-safe encryption are your new best friends. Just remember: in this wild data world, a little paranoia goes a long way.

From Paranoia to Productivity: AI-Powered Defenses that Actually Work
Let’s be honest: cybersecurity used to be a game of “who can panic the fastest.” If you’ve ever worked in a Security Operations Center (SOC), you know the drill—alerts pinging like popcorn, coffee mugs trembling, and the ever-present feeling that your data is one click away from starring in its own breach headline. But, thanks to the rise of AI cybersecurity adoption, there’s a new sheriff in town. And this one doesn’t need sleep, snacks, or even a bathroom break.
AI in threat hunting is basically the IT equivalent of finally being able to finish your coffee while it’s still hot. No more whack-a-mole with malware—AI-powered tools are now sifting through mountains of logs, spotting anomalies, and flagging threats faster than you can say “phishing email.” Research shows that AI cybersecurity productivity is on the rise, especially as more organizations embrace these tools in 2025. SOC teams are reporting less burnout, more uptime, and—wait for it—actual evenings spent outside the office. Miracles do happen.
But before you start planning your early retirement, let’s talk about the perks and pitfalls. AI cybersecurity benefits are real: faster threat analysis, smarter prioritization, and a noticeable boost in job satisfaction. As Kevin Mandia put it,
AI has empowered cybersecurity teams to fight smarter, not harder.
And who doesn’t want to fight smarter? (Or, at the very least, not harder.) AI-driven tools can analyze threats at lightning speed, automate repetitive tasks, and even predict where the next attack might come from. It’s like having a digital sidekick—one that never asks for a raise or steals your lunch from the fridge.
However, let’s not get too cozy with our AI pals just yet. While AI in threat hunting is a game-changer, it’s not a magic wand. Studies indicate that the productivity gains aren’t universal. Some organizations are still wrestling with uneven results, struggling to wrangle all that new tech into something that actually works. Sometimes, it’s like giving a toddler a jetpack—sure, it’s fast, but you really need to keep an eye on where it’s going.
Here’s where things get interesting (and a little bit wild): AI is evolving so quickly that it’s not just defending against threats—it’s creating new ones. AI-driven malware can mutate in real-time, making traditional threat hunting feel a bit like bringing a butter knife to a laser fight. Meanwhile, AI-generated phishing attacks are getting so good that even your most paranoid colleague might click “open.” (Don’t worry, we’ve all been there.)
So, what’s the secret sauce? Governance. Without clear policies and oversight, AI can go from superhero to supervillain faster than you can say “shadow AI.” Research shows that organizations with strong governance frameworks see the most AI cybersecurity benefits—think faster response times, less burnout, and fewer existential crises in the break room. But those who skip the rules? Well, let’s just say productivity gains can vanish quicker than your lunch during a long meeting.
Let’s break down the current state of AI cybersecurity adoption and productivity:
| Trend | Impact |
|---|---|
| AI cybersecurity adoption is rising in 2025 | More organizations are integrating AI tools into their SOCs |
| AI improves threat prioritization and SOC efficiency | Faster detection, smarter responses, less burnout |
| Productivity gains are not universal | Some organizations still face major struggles with implementation |
In the end, AI cybersecurity adoption is about more than just fancy algorithms and shiny dashboards. It’s about giving real people—yes, even the ones who hoard all the good snacks—a fighting chance against ever-evolving threats. With the right tools, policies, and a dash of common sense, you can finally trade paranoia for productivity. And maybe, just maybe, get home before sunset.
So, next time you see your AI-powered defense system working overtime, raise your (still-warm) coffee mug and remember: you’re not just surviving the cyber wilds—you’re thriving. And if you’re lucky, you might even get to keep your lunch.
TL;DR: AI cybersecurity is flipping cybersecurity upside down—for better and for perplexing. The trick? Use those AI tools wisely, keep an eye on shadowy digital tricks, and always double-check before opening that ‘urgent’ email. Your data deserves a bodyguard with a sense of humor.

